| Michael Horowitz |
Home => While We Were Sleeping
|
| Michael Horowitz |
Home => While We Were Sleeping
|
| [Formatted for Printing] | From the personal web site of Michael Horowitz |
June 29, 2020 | Updated July 3, 2020
To understand this blog, you need to understand DNS. My RouterSecurity.org website offers both a long and short explanation. TLDR: DNS translates the names of computers on the Internet that humans use (i.e. www.cnn.com) into the numbers (IP addresses) that computers actually use to communicate.
DNS is changing. The legacy format (UDP on port 53) has worked well for decades, but there was no encryption. The newer format (DoT and DoH) uses SSL/TLS to encrypt DNS requests. Most operating systems do not yet support encrypted DNS, but Android has been on the leading edge of this change. Both Android 9 and 10 have a feature called Private DNS which offers encrypted DNS system-wide. For older versions of Android, Google has an app called Intra that adds encrypted DNS to Android 6, 7 and 8.
I often use Intra on Android 9 and 10 because it offers a feature that Private DNS lacks - logging. These logs are the basis for this blog.
USING INTRA
After installing the Intra app, you enable it with the On/Off slider shown below.
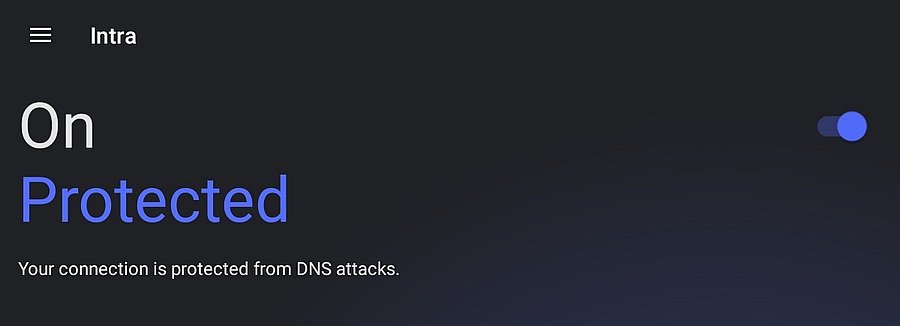
The bottom portion of the Intra home screen is shown below. The System Details section shows which encrypted DNS server is being used and offers an option to "Show recent queries" which creates the DNS activity log. In the screen shot, Intra is using NextDNS for encrypted DNS, more on that below.
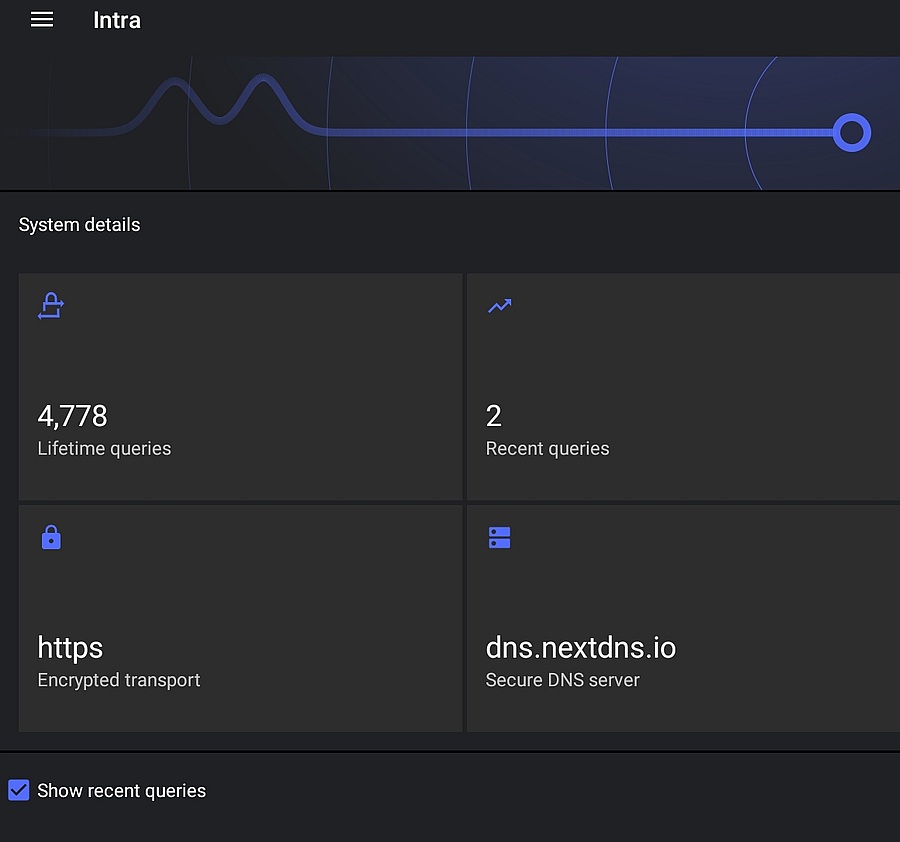
Most of the time, the logging of DNS requests is pretty boring stuff, but it gets much more interesting when the device is off. Not off off of course; normal off, which is perhaps better described as sleeping or suspended. What really piqued my interest, was looking at a DNS log one morning after the device had spent the night not only suspended but also off-line. Literally, while I was sleeping.
Needless to say, Intra was not the only thing running while the tablet (made by Samsung, running Android 9) should have been resting.
WHILE I WAS SLEEPING
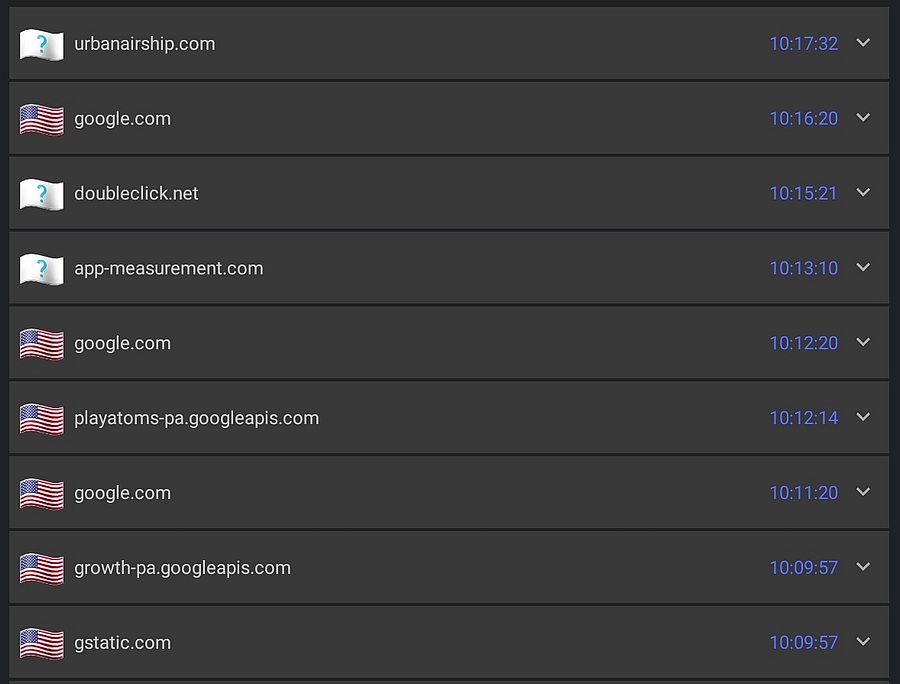
Our first example of the Intra DNS log is shown below. The exclamation point in the yellow triangle is due to the device being off-line.
That it tried to contact Samsung and Google is not a big surprise. Doubleclick.net and crashlytics.com are just the sort of ads and tracking that NextDNS blocks (more on this soon).
FACEBOOK?
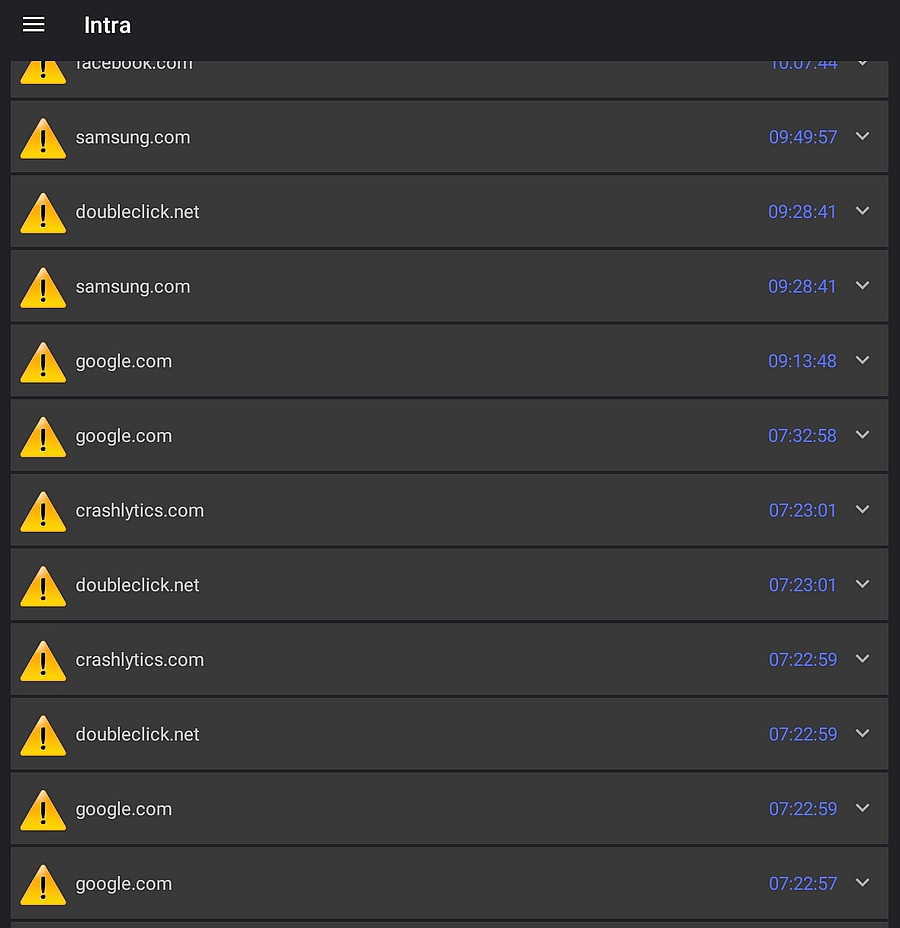
The log excerpt below is where things get really interesting. Facebook. Facebook. Facebook.
Sure, Facebook spies on us, this is common knowledge. Still, it's one thing to know it and another to see it in this DNS activity log. And, to see it on a tablet that is both off-line and suspended.
What makes this really creepy is that I don't use Facebook. Not only is the Facebook app itself not installed, no apps made by Facebook owned companies are installed. No WhatsApp, no Instagram, no nothing. The tablet has never had any Facebook related app installed. And yet, this.
Clearly, I have installed a traitor. A non-Facebook app is doing Facebook's spying for them. Facebook is like a sponge, trying to suck up information about all of us.
Below is another excerpt from the DNS log showing that Facebook is not the only destination contacted by insistent apps. Again, the tablet was both suspended and off-line when this log was created.
NEXTDNS BLOCKING SOME DOMAINS
Technically, all the logs above were harmless, as the device was off-line. For protection from being spied on while on-line, I am a big fan of NextDNS.
The Intra log below has no yellow triangles because the tablet was on-line. The American flag icon on the left indicates that the computer being contacted is in the US. The interesting thing here are the question marks in the white flags. These DNS queries were blocked by NextDNS. Some of the domains are for advertising, others are trackers (a.k.a spies).
The log below really shows the power of NextDNS domain blocking. Blocked blocked blocked. Facebook too.
And, another example of NextDNS blocking assorted ads and trackers.
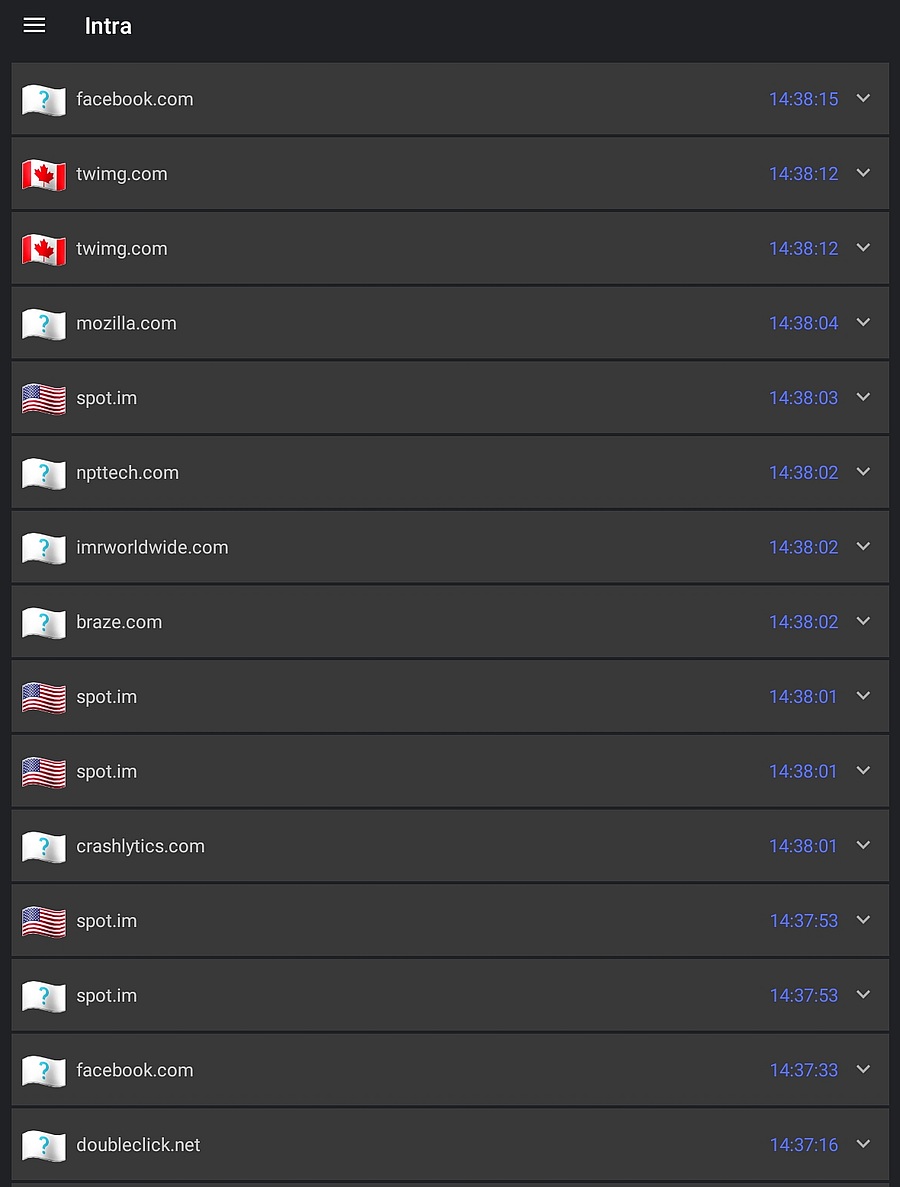
The Intra log below, from a different day, shows NextDNS blocking multiple trackers in the same second. Yet another indication of just how pervasive tracking is, at least on Android. (added July 3, 2020)
A LIMITATION OF INTRA LOGGING
One limitation of the logging feature of Intra is that, by default, it does not display the full DNS name. Below we see that it blocked disqus.com and then immediately thereafter allowed it. In, literally, the same second it seems like it made two different decisions (good vs. bad) on the same domain.
To understand this, we need more information. Clicking/pressing on the downward pointing triangle on the far right, shows the full details. That is, it shows the full DNS name that was requested, which includes the sub-domain. NextDNS blocked glitter.services.disqus.com but allowed realtime.services.disqus.com.
NEXTDNS LOGGING
NextDNS has its own Android app, but there is no logging feature. NextDNS does offer logging, but only on its website. A sample of the NextDNS log from their website is shown below. The log entries were generated by the CNN.com home page.
Thankfully, it shows full DNS names. The vertical red bar to the left of the name indicates that the DNS request was blocked. If you hover the mouse over the red circle with the white "i" inside, it shows information on why the name was blocked. In the case of agility.cnn.com it was blocked by a blocklist called "nextdns-recommended". Hovering the mouse over the blue circles provides much more information about that particular domain and sub-domain.
As with Intra, the activity log is optional with NextDNS. Unlike Intra, it is configurable in a number of ways. And, NextDNS can log DNS activity from more than one device.
Much of NextDNS is configurable. If it blocks something you want to see, there is a whitelist. If it is allowing something you want blocked, there is a blacklist. If you want something blocked on one device but not blocked on another device, it can do that too. It even makes a special case of blocking Facebook.
When it comes to NextDNS, I am just a customer. That said, it seems like the greatest thing since sliced bread. And since mobile devices try to spy on you even when both you and the device are sleeping, it seems like its ad and tracker blocking are a necessity.
| | ||
| Home => While We Were Sleeping | TOP | |
| michael--at--michaelhorowitz.com | Last Updated: July 4, 2020 2PM UTC | ||

Copyright 2001-2025 |
Copyright 2001-2025 |